In a ransomware attack, a piece of malicious software paralyzes your computer until you pay the demanded sum. It’s a scary situation that will cost you money and time.
When a ransomware attack hits a hospital, it can even cost lives: A recent lawsuit in Alabama alleges that a newborn’s death resulted from the crippling effects of a ransomware attack that took the hospital offline for eight days.
Ransomware attacks are a relatively easy way to milk money from victims. The larger the target, the more potential for big payouts. And these hackers don’t care who gets hurt.

“We were quite surprised because people thought that during Covid hackers would leave the healthcare vertical alone, but the reality is a 200 percent increase in such attacks during Covid. Criminals just want to make money,” says Leon Lerman, CEO and cofounder of four-year-old Israeli healthcare cybersecurity company Cynerio.
“If you can’t trust a hospital, when you’re in your most vulnerable state, that’s really concerning,” adds Lerman. “It’s a different game than with credit card or identity theft.”
Healthcare under attack
“Healthcare is one of the industries most targeted by cyberattacks,” admits Amir Magner, president and founder of CyberMDX, another Israeli healthcare cybersecurity specialist.
“According to a recent report, a total of 82 ransomware incidents against the health sector have occurred in 2021 worldwide, with 60 percent of them impacting the United States,” Magner tells ISRAEL21c.
The Tel Aviv-based company finds that one in six US data breaches occurs in hospitals. The average cost of each healthcare breach is $9 million.
“Recent attacks from notorious gangs such as REvil or Conti on hospitals have accounted for 30 percent of all significant data breaches at an estimated cost of $21 billion in 2020 alone,” says Magner, citing an Ipsos survey, “Perspectives in Healthcare Security Report” sponsored by CyberMDX and medical device maker Philips.
While the Alabama incident illustrates the worst-case scenario, the worst in terms of magnitude was a ransomware attack that shut down California’s Scripps Health hospital group last May.
Patient care was compromised for about a month until the damage was repaired, and several lawsuits seek compensation for non-protection of health records during that time.
“As of June 30th, we estimate total lost revenues to be $91.6 million and incremental costs incurred to address the cyber security incident and recovery were estimated at $21.1 million,” a Scripps earnings report said. Only a fraction of the total amount was covered by cyber insurance.

How hospital cyberattacks harm you
“In sectors such as banking or insurance, the worst outcome for the customer is largely the theft of personal data. In healthcare, the stakes are much higher,” says Magner.
“One of the reasons that healthcare is among the most targeted industries is that personal health records are the most highly valued on the black market. The data stolen and sold may be enough for hackers to steal identities or any number of other nefarious activities,” he explains.
“Many hospitals have experienced a significant shutdown or breakdown of critical departments, systems and healthcare services due to cyberattacks, and these could potentially not only endanger people’s personal health information, but also their lives or those of their loved ones.”
How does a healthcare organization get breached?
“The threats against healthcare agencies are rapidly evolving, with new vectors being discovered daily,” says Jonathan Langer, cofounder and CEO of Medigate, established in 2017, with offices in Tel Aviv, California and New York. “Some of the well-known methods we have seen, in addition to ransomware, are malware and spyware, phishing and spear phishing, and the distributed denial of service. There are many routes into a healthcare technology environment, so vigilance and careful planning are needed to ensure attacks are stopped before they become harmful,” Langer tells ISRAEL21c.
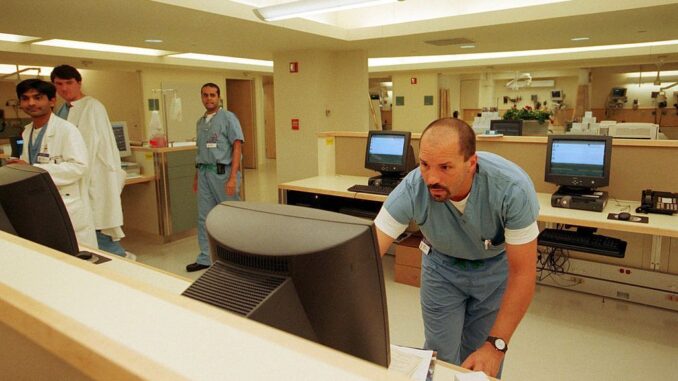
Many breaches originate from a medical device connected to the Internet or the hospital’s internal network – MRI machines, infusion pumps, ventilators and more.
“Connected devices and systems are a huge boon for hospitals, enabling improved patient care. However, every connected device is a potential entry point for bad actors if we fail to protect them adequately,” says Magner, whose company estimates that 61 percent of medical devices are at persistent cybersecurity risk.
It’s not just medical devices. Laptop computers, HVAC systems, smart elevators and refrigerators also can be entry points, adds Lerman.
“An attack likely starts on the IT side. It may be a nursing-station computer where someone clicks on an attachment in an email,” Lerman explains.
“It infects the laptop and moves across the hospital network to connected devices that often have older operating systems. From that moment of encryption, the machine is not operable,” Lerman explains.
Wireless networks, telehealth systems and remote work situations, in wide use since the start of the Covid-19 pandemic for many good reasons, unfortunately give hackers more opportunities as well.

Some hackers use a third-party “watering hole” attack to infect websites of companies that directly interface online with hospitals, such as suppliers. From there, the infection spreads to the hospital.
So-called “ethical hackers” have demonstrated the possibility of sophisticated cyberattacks targeting a specific hospital device or even a specific patient, for example maliciously changing the dosage of an IV pump.
While there are no documented cases so far, “it’s more possible as devices get more and more connected,” says Lerman.
What are hospitals’ options after a breach?
After a ransomware attack, a hospital can choose to pay the ransom or pay the price of rebuilding the system and losing revenue and operating capacity during the fix – knowing that the hacker may target the same hospital repeatedly.
“Once computers or medical devices are affected, [most] hospitals will pay,” Lerman says. “If you lose files, you may have a backup. But if an MRI machine doesn’t work, every minute it’s offline you’re losing thousands of dollars. So you’ll pay the ransom to keep going.”
Investing in prevention theoretically makes the most sense. But the Ipsos survey revealed that even with roughly half of respondents experiencing an externally motivated shutdown in the six months prior to the survey, more than 60 percent of hospital IT teams have other spending priorities. Industry experts say three out of four hospitals do not have the budget and/or personnel to properly monitor their network.
Bad actors are aware of this.
“In comparison with other industries,” says Lerman, “hospitals have less security control and inhouse cybersecurity professionals. Hackers want to go where it’s easy.”

How do Israeli cybersecurity companies help?
Some healthcare cybersecurity companies work with medical device manufacturers to build premarket protection into their systems.
“You cannot install anything on those devices [postmarket] because it would void the warranty,” explains Lerman.
Others focus on solutions that are not device specific. Most of the latter companies help hospitals identify all its connected devices – not just the medical ones — and any threats they encounter.
“One of the largest problems today is that security teams within healthcare organizations lack visibility into their medical devices. You can’t protect what you can’t see and without this basic knowledge you cannot extend the proper protections across your devices,” CyberMDX’s Magner says.
Additional services may include risk management, alerts and actionable insights.
Cynerio’s Ramat Gan-based R&D team recently developed the first dedicated IoT attack detection and response module for devices in healthcare environments. This lets clients identify, contain and mitigate threats, and perform recovery forensics during downtime.
“We do risk reduction for every problem we find, on the device level or on the network level,” Lerman says.
While general cybersecurity companies can help keep healthcare institutions safe, a growing number are geared exclusively to hospital environments.
“If you have a ventilator with malware on it and you disconnect it from the network as a response measure, you need to know what you are doing so as not to cause harm,” says Lerman. “You need to understand medical workflows and the hospital ecosystem.”
Produced in association with Israel21C.
The post Hospital Cyberattack Is The New Pandemic; Here’s The Cure appeared first on Zenger News.